What is encrypted messaging compliance?
Encrypted messaging compliance is the practice of capturing, retaining, and supervising business communications sent over encrypted mobile messaging platforms — iMessage, WhatsApp, Signal, and others — in a manner that satisfies SEC, FINRA, and applicable record-keeping regulations. Any message related to client activity or firm business is considered a business communication, regardless of channel or how informal it may seem.
The “encrypted” part matters. These platforms were built with privacy in mind, which is why we use them - but it really makes compliance difficult. End-to-end encryption is a feature, not a flaw; it means only the sender and recipient can read the message on their devices. Because there’s no central point where messages pass through in readable form, there’s no obvious place for a firm to intercept and archive them. That’s where the compliance challenge begins.
The core requirements haven’t changed. Under SEC Rule 17a-4 and FINRA Rule 4511, broker-dealers must:
- Every client conversation — iMessage, WhatsApp, Signal, email — needs to be captured automatically. Not manually saved. Not forwarded somewhere. Captured.
- It needs to be stored in a format nobody can edit or delete after the fact. This is known as WORM (Write-One, Read Many) so the original message cannot be changed after being sent. The alternative is to have an audit-trail capability that permits the recreation of an original record.
- If a regulator asks for a thread from two years ago, you need to be able to produce it.
- Someone needs to be reviewing flagged messages for policy violations.
What has changed is where those business communications live. The answer is not in email.
Why enforcement shifted to off-channel messaging
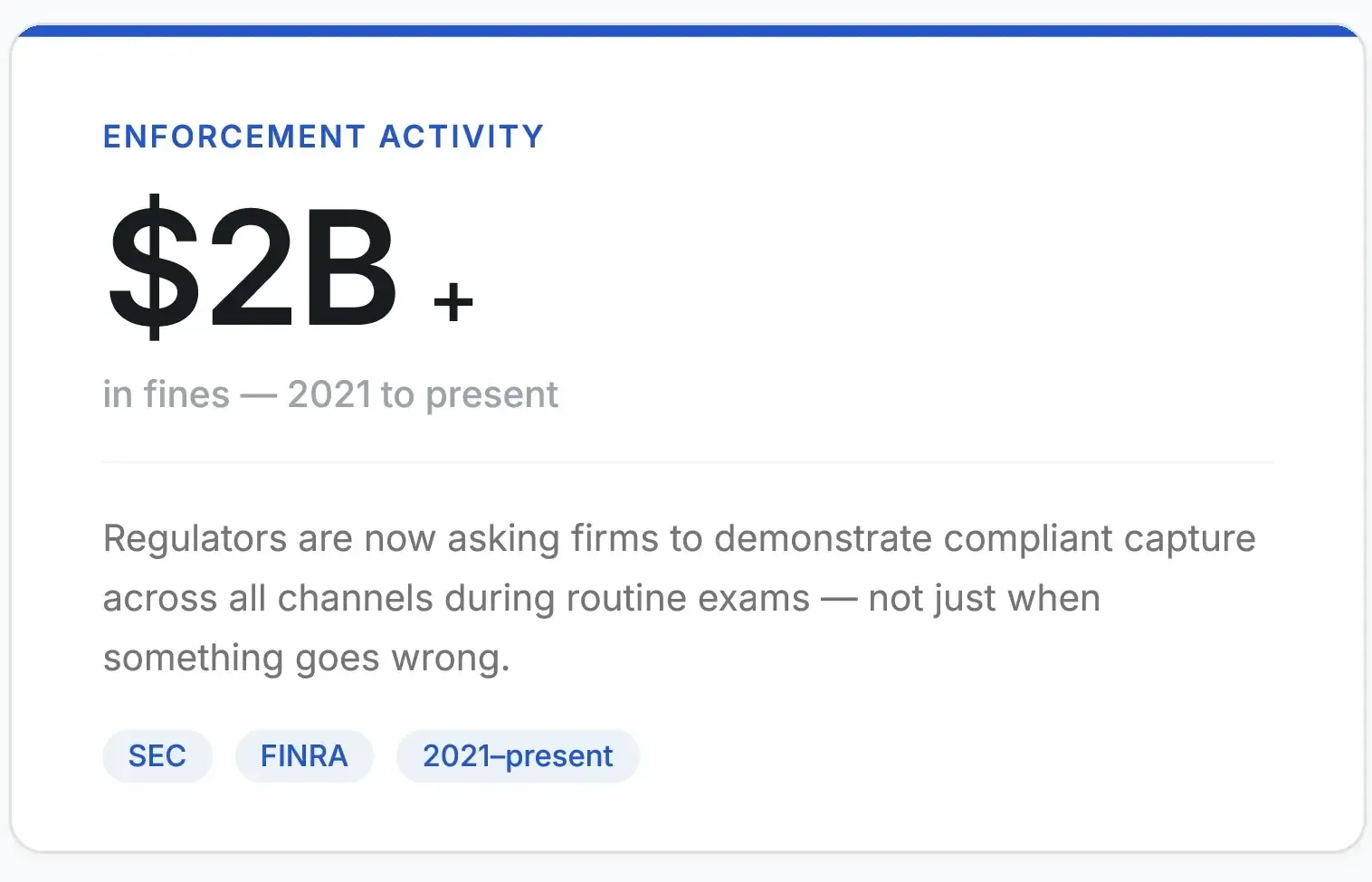
Regulators are no longer waiting for a whistleblower tip or a litigation hold to surface a missing message thread. They’re asking firms, during routine exams, to demonstrate that all business communications — across all platforms — are being captured and retained. Firms that can’t produce records from iMessage or WhatsApp are finding that “we have a policy against it” is not a sufficient answer when the evidence shows those platforms were used anyway.
When clients expect fast, convenient communications, employees use the tools their clients use, which is often encrypted messaging apps. And until recently, most compliance infrastructure couldn’t touch them.
That gap — between where conversations actually happen and what compliance systems can actually capture — is what regulators are now exploiting. Not through novel legal theories, but by simply asking for records that firms assumed were out of scope.
Recent events have made this gap more obvious. In 2025, TeleMessage, a vendor that sold a Signal-based archiving tool to government and financial clients, was breached. The breach revealed that the platform temporarily stored message content in plaintext during the capture, even though it was marketed as end-to-end encrypted (E2EE). The issue wasn’t encryption, but rather how the capture was implemented. To understand why implementation matters so much, you need to understand one thing about how encrypted messaging is fundamentally different from email.
The real archive gap isn’t encryption. It’s architecture.
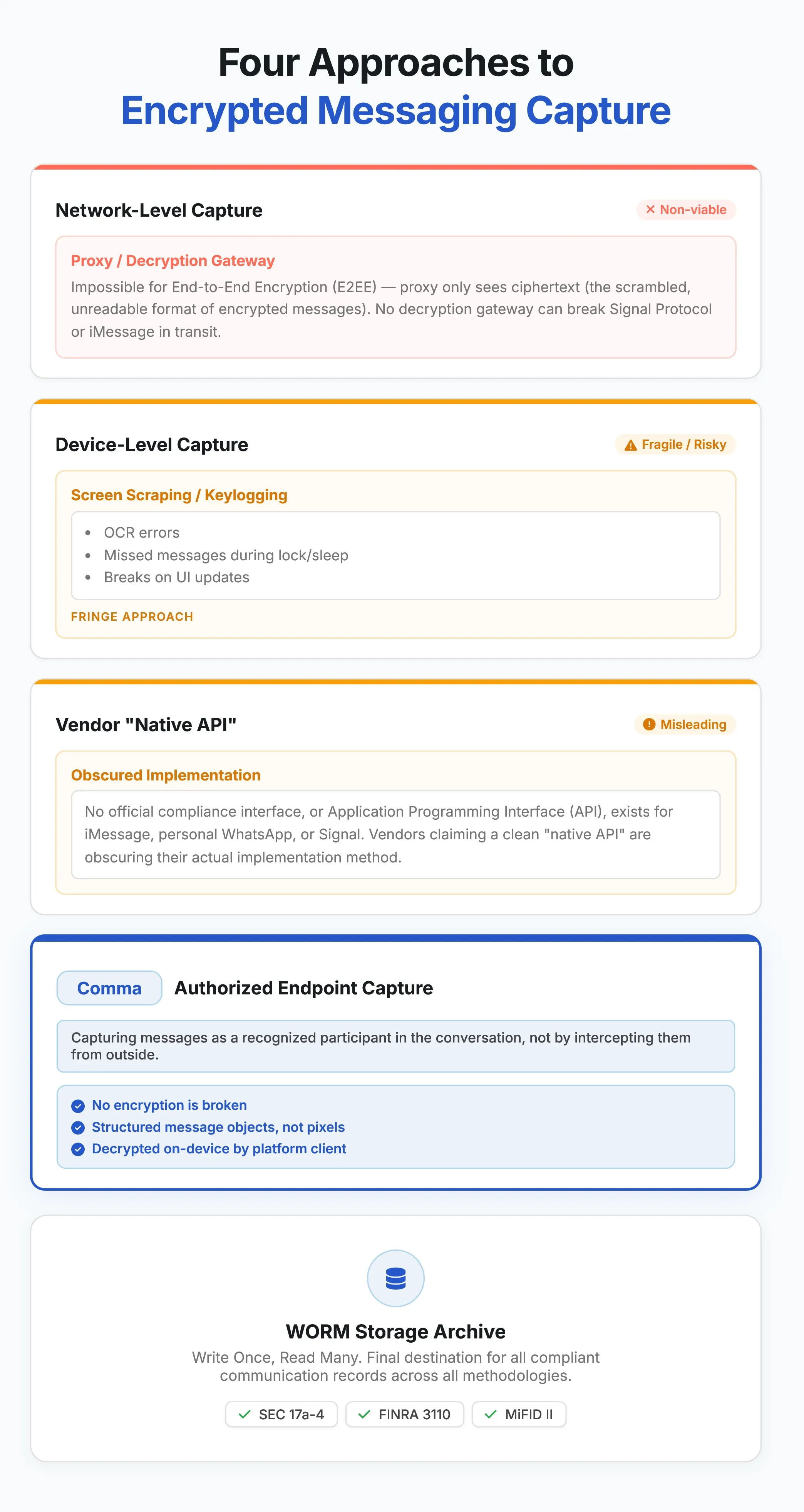
So, if these messages are end-to-end encrypted, how can any vendor actually capture them?
It’s tempting to frame encrypted messaging compliance as a technology problem — that end-to-end encryption makes capture impossible. That’s not accurate. The harder problem is architectural.
Most compliance platforms were designed for email. When vendors attempt to extend those platforms to capture iMessage or WhatsApp, they typically rely on one of two approaches:
1: The backup-dependent approach.
Messages are pulled from iCloud or device backups after the fact. This creates a risk window between when a message is sent and when it’s captured — a window during which messages can be edited, deleted, or simply never backed up.
The archive reflects what existed at the moment of retrieval, not necessarily what was originally sent.
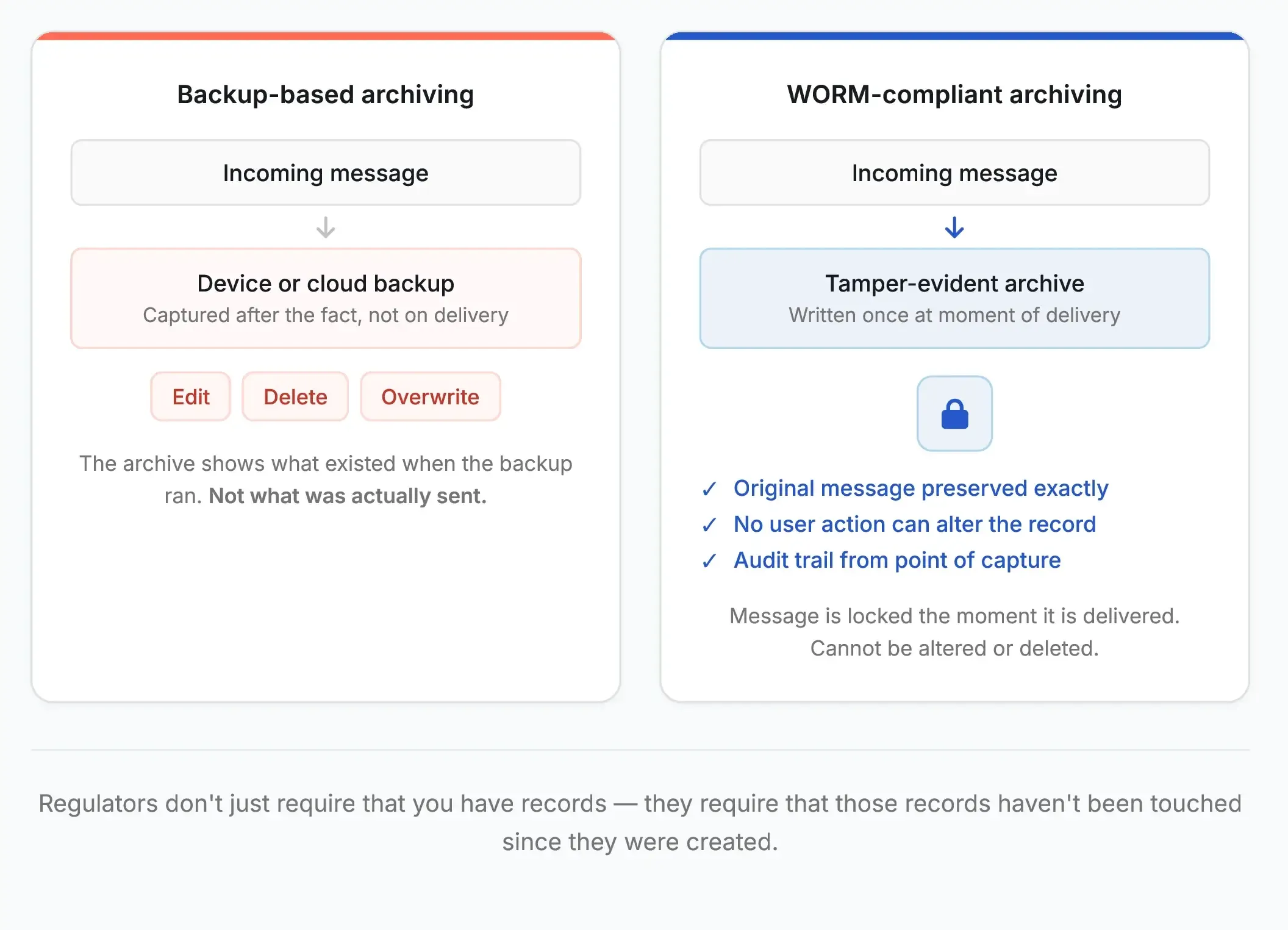
That distinction matters because WORM compliance isn’t just about what happens inside the archive. It’s about whether the record is complete and unaltered from the moment of creation.
2: The Mobile Device Management (MDM) approach.
The second approach is the Mobile Device Management (MDM) approach. Compliance software is installed directly on the employee’s phone, reading and copying messages in the background.
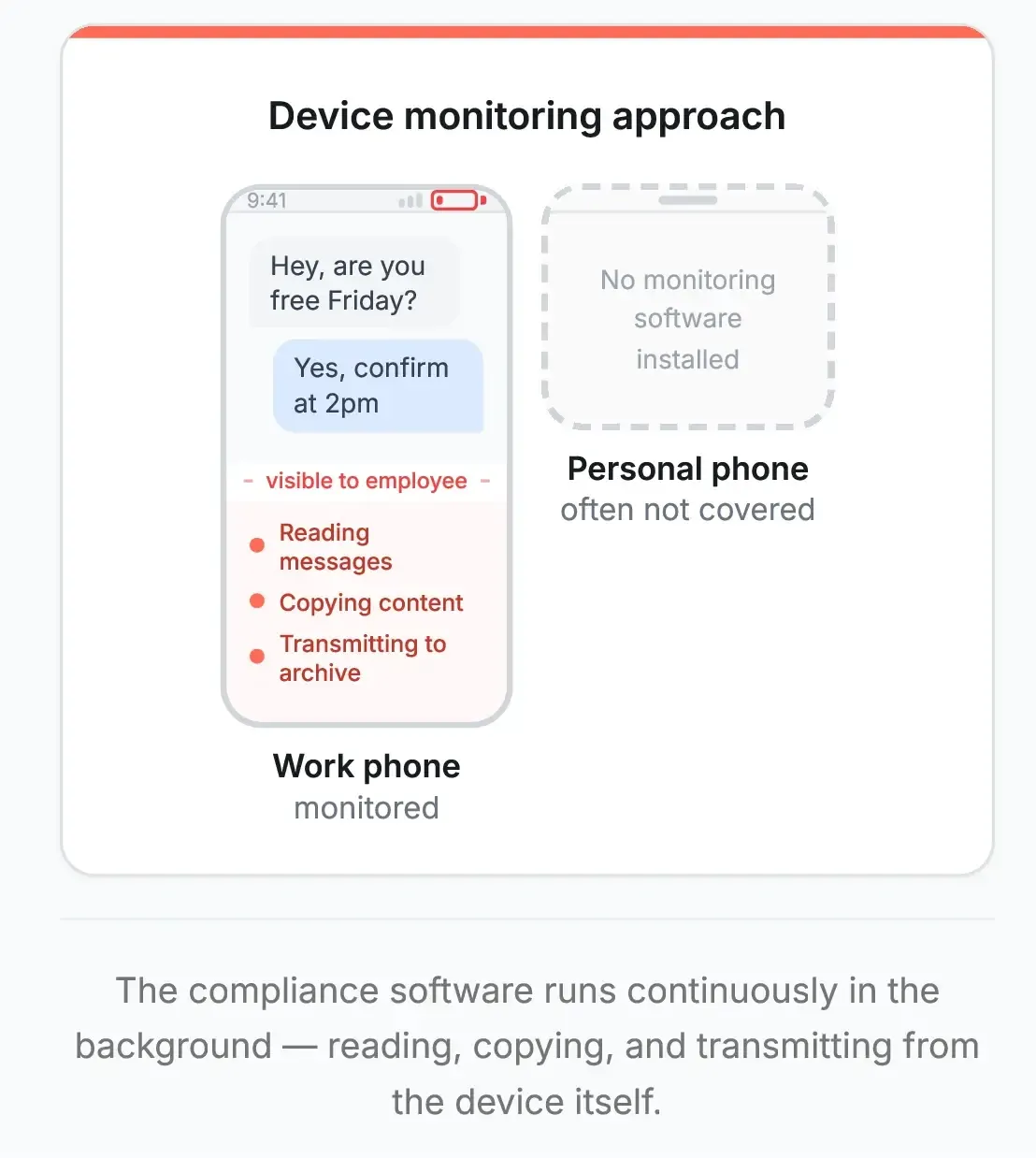
This raises immediate privacy concerns, creates IT (Information Technology) overhead, introduces battery and performance issues, and typically fails to capture messages from personal devices entirely—where the highest-risk conversations often occur.
Neither approach is compliant by design. Both require everything to go right, and thus create gaps when things don’t.
True encrypted messaging compliance requires capture at the point of delivery—before messages enter any mutable (changeable) consumer storage — and immediate write to WORM-compliant archives. Not eventually. Not after a backup runs. At the moment of transmission.
The channels that create the most compliance risk
iMessage
iMessage is the default communication app on every iPhone and Mac. It’s convenient, it’s fast, and it’s used for business constantly. No one is making a deliberate channel decision. Employees don’t switch to a compliant channel; they see a message, and they reply. That’s how iMessage becomes a business communication record.
The compliance challenge with iMessage is twofold. First, Apple’s architecture was built for consumers, not regulated firms. Messages can be edited and deleted. Backup settings are user-controlled. Second, most compliance vendors treat iMessage like SMS — either blocking it or capturing only a degraded version of the thread.
Comma Compliance captures iMessages independently of iCloud backups and device activity. No backup timing dependency. No user setting that can break the capture. No content gaps.
See how iMessage archiving works →
After the TeleMessage breach, the question firms started asking changed. The bar used to be simple: are you capturing messages? Now it’s harder to clear: how are you capturing them — and is there anything beyond a vendor’s word to prove it?
See our open-source WhatsApp capture →
Signal
Signal is the gold standard for private communication. Its end-to-end encryption is technically rigorous, designed so that only the sender and recipient can read a message, on their devices. That’s exactly why security-conscious users prefer it, and also exactly why some compliance vendors have struggled to handle it without compromising those properties.
The lesson isn’t that Signal can’t be archived. It’s how you archive it that matters enormously.
See our open-source Signal capture →
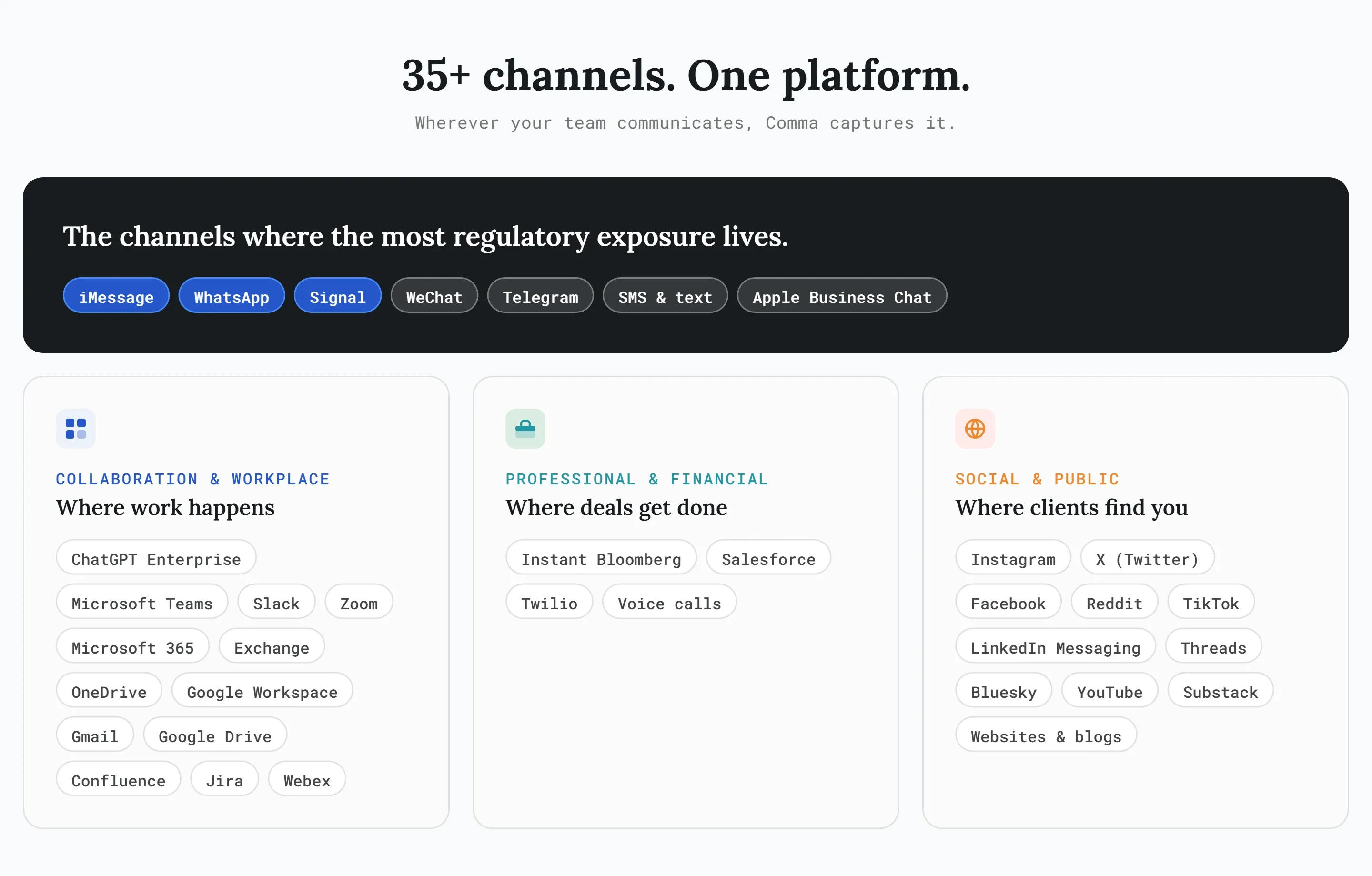
LinkedIn, WeChat, Telegram, and 35+ more
iMessage, WhatsApp, and Signal tend to drive headlines, but the off-channel risk landscape is wider. Bloomberg Chat, WeChat, Telegram in personal use contexts — each represents a potential gap. A compliant encrypted messaging program accounts for where conversations actually happen, not just where firms prefer they happen.
What compliant capture looks like
Compliant capture has a few non-negotiable properties:
Capture at the point of delivery.
Messages should be written to immutable storage at the point of delivery — simultaneously with being received on the device. If a message is edited or deleted afterward, the archive already holds what was originally sent.
Capture that doesn’t rely on user settings.
Capture should not depend on iCloud backup settings, device storage limits, screen lock status, battery level, or any other variable the user controls. When compliant archiving requires everything to go right on a user device, it will eventually fail.
WORM storage from the start.
Write-once, read-many storage isn’t a checkbox at the end of the workflow. It should be where messages land immediately. The gap between capture and immutable storage is a compliance gap.
Auditability.
You should be able to answer the question “how was this message captured?” with something more substantive than a vendor’s marketing materials. Source code that can be inspected, forked, and independently verified is a qualitatively different level of assurance than a brochure.
See why we open sourced our Signal and WhatsApp capture code →
Questions to ask any encrypted messaging compliance vendor
Before trusting a vendor with your off-channel message archive, ask these questions.
Due Diligence
Five questions to ask before you sign
- 01
When exactly is a message captured - the moment it's sent, or later?
- 02
What can cause a message to be missed - and would I know if that happened?
- 03
If an employee deletes a message, is it still in the archive?
- 04
Can you show me how the capture actually works - not just describe it?
- 05
If I get an exam request, can I pull the records from your platform directly?
How Comma Compliance covers the hardest channels
Good encrypted messaging compliance requires capture at the point of delivery, storage nobody can alter, and coverage for every channel your team actually uses. Here’s how Comma Compliance handles each one.
For iMessage:
Works on the iPhone your clients already text you on. Nothing changes about how you or your clients communicate — capture happens automatically in the background, independent of iCloud and without touching anything on your phone. No backup timing risk, and no battery drain.
For WhatsApp:
Your clients don’t need to download anything or change how they message you. Capture happens on your end. The conversation looks and feels identical to them. If you’d like to see our real-time capture with open-source connector code, it’s publicly available on GitHub under Apache 2.0. Auditors, CISOs, and engineering teams can inspect every line of capture logic.
For Signal:
Signal’s privacy properties stay intact — for you and your clients. Capture happens at the point of delivery without compromising how Signal works. Comma’s approach doesn’t compromise Signal’s encryption model.
For everything else:
35+ channels supported, from Bloomberg Chat to WeChat, managed from a single dashboard. AI-powered policy matching and case management built for regulatory exams means every case arrives exam-ready, with full message history, timestamps, review notes, and a complete resolution trail, all organized and exportable on demand. Personal and business contact filtering keeps employee privacy intact throughout.
The bottom line on encrypted messaging compliance
Encrypted messaging isn’t a compliance edge case. It’s where a significant share of business communication happens, and where the largest regulatory exposure now lives.
The firms that get this right aren’t the ones with the most restrictive messaging policies. They’re the ones that stopped treating mobile channels as a problem to ban and started treating them as a reality to capture — with architecture that actually works.
That means real-time capture. WORM storage from the start. Auditability you can demonstrate, not just assert. And coverage for every channel your team uses, not just the ones your legacy vendor was designed for.
Related reading
- Consumer Messaging Compliance Archiving Why disappearing messages, view-once media, and feature velocity keep making consumer messaging compliance harder.
- The TeleMessage/Signal Clone Scandal: A Full Timeline
- Why We Open-Sourced Our WhatsApp & Signal Capture Code
- iMessage Compliance: Why iCloud-Based Archiving Falls Short
